Cisco Easy VPN is a convenient method to allow remote users to
connect to your network using IPsec VPN tunnels. The advantage of Easy
VPN is that you don’t have to worry about all the IPSEC security details
on the client side. Just configure the remote router, group name,
username /password and you are ready to go. In this tutorial I’ll show
you how to configure Easy VPN on a Cisco IOS router and we’ll use the
Cisco VPN client to setup the connection.
This is the topology that we’ll be using:
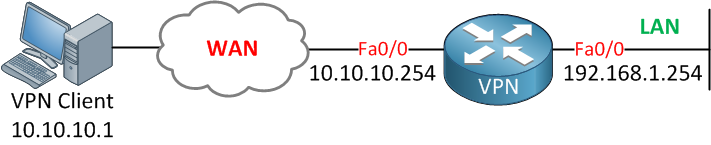
A single router configured for Easy VPN and a computer running Cisco’s VPN client software. Let’s start with the router configuration!
For the VPN group we’ll have to configure a number of items. First of all there’s a password but you can also specify some client specific parameters like a DNS server, WINS server, how many users are able to connect etc. Here’s how to do it:
The next step is to configure a transform-set. This is where we configure our phase 2 authentication and encryption settings:

Once you hit save and try to connect the router will ask you for your credentials:
 Enter
your username and password, hit OK and you will be connected! I hope
this tutorial has been helpful to you, if you have any questions feel
free to leave a comment!
Enter
your username and password, hit OK and you will be connected! I hope
this tutorial has been helpful to you, if you have any questions feel
free to leave a comment!
This is the topology that we’ll be using:
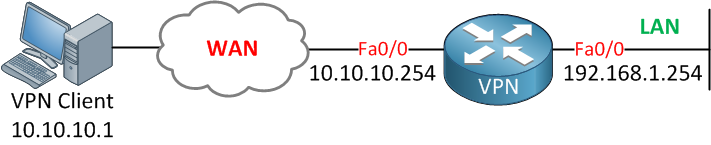
A single router configured for Easy VPN and a computer running Cisco’s VPN client software. Let’s start with the router configuration!
Router Configuration
First we need to enable AAA for authentication, authorization and accounting. We can use this for local authentication (usernames and passwords on the router) or use an external RADIUS server for this.
Be aware that once you enable AAA that your
authentication settings of the console and VTY lines are now controlled
by AAA. Make sure you don’t lock yourself out of the router or
accidently allow VPN users to access your router.
For simplicity, we’ll use local authentication.VPN(config)#aaa authentication login default local
VPN(config)#aaa authentication login VPNUSER local
VPN(config)#aaa authorization exec default local
VPN(config)#aaa authorization network VPNGROUP localVPN(config)#username VPNUSER password CISCOVPN(config)#crypto isakmp policy 1
VPN(config-isakmp)#authentication pre-share
VPN(config-isakmp)#encryption aes
VPN(config-isakmp)#group 2For the VPN group we’ll have to configure a number of items. First of all there’s a password but you can also specify some client specific parameters like a DNS server, WINS server, how many users are able to connect etc. Here’s how to do it:
VPN(config)#crypto isakmp client configuration group VPNGROUP
VPN(config-isakmp-group)#key 0 CISCO
VPN(config-isakmp-group)#dns 192.168.1.253
VPN(config-isakmp-group)#wins 192.168.1.253
VPN(config-isakmp-group)#pool VPNPOOL
VPN(config-isakmp-group)#max-users 10
VPN(config-isakmp-group)#netmask 255.255.255.0
VPN(config-isakmp-group)#domain NETWORKLESSONS.LOCALVPN(config)#ip local pool VPNPOOL 192.168.2.100 192.168.2.200The next step is to configure a transform-set. This is where we configure our phase 2 authentication and encryption settings:
VPN(config)#crypto ipsec transform-set TRANSFORMSET esp-aes esp-sha-hmacVPN(config)#crypto isakmp profile ISAKMPPROFILE
VPN(conf-isa-prof)#match identity group VPNGROUP
VPN(conf-isa-prof)#client authentication list VPNUSER
VPN(conf-isa-prof)#isakmp authorization list VPNGROUP
VPN(conf-isa-prof)#client configuration address respond
VPN(conf-isa-prof)#virtual-template 1VPN(config)#crypto ipsec profile VPNPROFILE
VPN(ipsec-profile)#set transform-set TRANSFORMSET
VPN(ipsec-profile)#set isakmp-profile ISAKMPPROFILEVPN(config)#interface virtual-template 1 type tunnel
VPN(config-if)#ip unnumbered fa0/1
VPN(config-if)#tunnel mode ipsec ipv4
VPN(config-if)#tunnel protection ipsec profile VPNPROFILE
When your router is also configured for
NAT, don’t forget to configure your access-list so your VPN traffic is
not translated when it leaves the router.
Client Configuration
We already did the hard work on the router so the client side is pretty straightforward. Create a new profile and enter the group name and password that we just configured:
Once you hit save and try to connect the router will ask you for your credentials:
 Enter
your username and password, hit OK and you will be connected! I hope
this tutorial has been helpful to you, if you have any questions feel
free to leave a comment!
Enter
your username and password, hit OK and you will be connected! I hope
this tutorial has been helpful to you, if you have any questions feel
free to leave a comment!
Belle solution pour la configuration VPN .
RépondreSupprimertop10-bestvpn.com
Merci.
RépondreSupprimerCette configuration fonctionne très bien.
Ce poste a vraiment aidé avec la solution.
10webhostingservice.com